A Portal to a Portal
Geeking in technology since 1985, with IBM Development, focused upon Docker and Kubernetes on the IBM Z LinuxONE platform In the words of Dr Cathy Ryan, "If you don't write it down, it never happened". To paraphrase one of my clients, "Every day is a school day". I do, I learn, I share. The postings on this site are my own and don’t necessarily represent IBM’s positions, strategies or opinions. Remember, YMMV https://infosec.exchange/@davehay
Saturday 17 February 2024
Visual Studio Code - Wow 🙀
Saturday 30 December 2023
Getting started with Python in Jupyter Notebooks
Saturday 4 November 2023
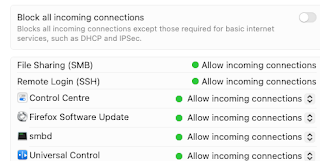
More on macOS SMB sharing
Monday 23 October 2023
Why I can't install jq on Ubuntu 20.04
Distributor ID: Ubuntu
Description: Ubuntu 20.04.6 LTS
Release: 20.04
Codename: focal
Building dependency tree
Reading state information... Done
E: Unable to locate package jq
# newer versions of the distribution.
deb http://us.archive.ubuntu.com/ubuntu focal main
# deb-src http://us.archive.ubuntu.com/ubuntu focal main restricted
## Major bug fix updates produced after the final release of the
## distribution.
deb http://us.archive.ubuntu.com/ubuntu focal-updates main
# deb-src http://us.archive.ubuntu.com/ubuntu focal-updates main restricted
## N.B. software from this repository is ENTIRELY UNSUPPORTED by the Ubuntu
## team. Also, please note that software in universe WILL NOT receive any
## review or updates from the Ubuntu security team.
# deb-src http://us.archive.ubuntu.com/ubuntu focal universe
# deb-src http://us.archive.ubuntu.com/ubuntu focal-updates universe
## N.B. software from this repository is ENTIRELY UNSUPPORTED by the Ubuntu
## team, and may not be under a free licence. Please satisfy yourself as to
## your rights to use the software. Also, please note that software in
## multiverse WILL NOT receive any review or updates from the Ubuntu
## security team.
# deb-src http://us.archive.ubuntu.com/ubuntu focal multiverse
# deb-src http://us.archive.ubuntu.com/ubuntu focal-updates multiverse
## N.B. software from this repository may not have been tested as
## extensively as that contained in the main release, although it includes
## newer versions of some applications which may provide useful features.
## Also, please note that software in backports WILL NOT receive any review
## or updates from the Ubuntu security team.
deb http://us.archive.ubuntu.com/ubuntu focal-backports main
# deb-src http://us.archive.ubuntu.com/ubuntu focal-backports main restricted universe multiverse
## Uncomment the following two lines to add software from Canonical's
## 'partner' repository.
## This software is not part of Ubuntu, but is offered by Canonical and the
## respective vendors as a service to Ubuntu users.
# deb http://archive.canonical.com/ubuntu focal partner
# deb-src http://archive.canonical.com/ubuntu focal partner
deb http://us.archive.ubuntu.com/ubuntu focal-security main
# deb-src http://us.archive.ubuntu.com/ubuntu focal-security main restricted
# deb-src http://us.archive.ubuntu.com/ubuntu focal-security universe
# deb-src http://us.archive.ubuntu.com/ubuntu focal-security multiverse
# deb-src http://us.archive.ubuntu.com/ubuntu focal universe
# deb-src http://us.archive.ubuntu.com/ubuntu focal-updates universe
# deb-src http://us.archive.ubuntu.com/ubuntu focal-backports main restricted universe multiverse
# deb-src http://us.archive.ubuntu.com/ubuntu focal-security universe
deb http://us.archive.ubuntu.com/ubuntu focal universe
deb http://us.archive.ubuntu.com/ubuntu focal-updates universe
deb http://us.archive.ubuntu.com/ubuntu focal-security universe
EOF
and tried again: -
Building dependency tree
Reading state information... Done
The following additional packages will be installed:
libjq1 libonig5
The following NEW packages will be installed:
jq libjq1 libonig5
0 upgraded, 3 newly installed, 0 to remove and 0 not upgraded.
Need to get 313 kB of archives.
After this operation, 1,062 kB of additional disk space will be used.
Get:1 http://us.archive.ubuntu.com/ubuntu focal/universe amd64 libonig5 amd64 6.9.4-1 [142 kB]
Get:2 http://us.archive.ubuntu.com/ubuntu focal-updates/universe amd64 libjq1 amd64 1.6-1ubuntu0.20.04.1 [121 kB]
Get:3 http://us.archive.ubuntu.com/ubuntu focal-updates/universe amd64 jq amd64 1.6-1ubuntu0.20.04.1 [50.2 kB]
Fetched 313 kB in 1s (440 kB/s)
Selecting previously unselected package libonig5:amd64.
(Reading database ... 108600 files and directories currently installed.)
Preparing to unpack .../libonig5_6.9.4-1_amd64.deb ...
Unpacking libonig5:amd64 (6.9.4-1) ...
Selecting previously unselected package libjq1:amd64.
Preparing to unpack .../libjq1_1.6-1ubuntu0.20.04.1_amd64.deb ...
Unpacking libjq1:amd64 (1.6-1ubuntu0.20.04.1) ...
Selecting previously unselected package jq.
Preparing to unpack .../jq_1.6-1ubuntu0.20.04.1_amd64.deb ...
Unpacking jq (1.6-1ubuntu0.20.04.1) ...
Setting up libonig5:amd64 (6.9.4-1) ...
Setting up libjq1:amd64 (1.6-1ubuntu0.20.04.1) ...
Setting up jq (1.6-1ubuntu0.20.04.1) ...
Processing triggers for man-db (2.9.1-1) ...
Processing triggers for libc-bin (2.31-0ubuntu9.12) ...
jq-1.6
"friends": [
{
"givenName": "Dave",
"familyName": "Hay"
},
{
"givenName": "Homer",
"familyName": "Simpson"
},
{
"givenName": "Marge",
"familyName": "Simpson"
},
{
"givenName": "Lisa",
"familyName": "Simpson"
},
{
"givenName": "Bart",
"familyName": "Simpson"
}
]
}
Thursday 15 June 2023
macOS to macOS File Sharing - Don't work, try The IT Crowd
I use File Sharing between two Macs on the same network, both running the latest macOS 13.4 Ventura.
For some strange reason I wasn't able to access one Mac - a Mini - from the other - a MacBook Pro.
As is always the case, the internet solved it for me: -
Fix File Sharing Not Working in MacOS Ventura
TL;DR; turn it off, and on again
Yes, The IT Crowd strikes again
Having said that, Dan Moren, he of Six Colours, acclaimed author AND MacBreak Weekly host, deserves full thanks for directing me to macOS' built-in firewall tool: -
/usr/libexec/ApplicationFirewall/socketfilterfw --listapps
Solving a file sharing mystery: Why one Mac can’t see another
Whilst the TIOAOA trick worked this time, who knows what I'll need next time ...
Monday 22 May 2023
On the subject of aliases ...
(a) typing more stuff
(b) looking in my notes to remember what I need, in order to type more stuff
Using 1Password to store API keys ...
Following on from my earlier post: -
Wow, why have I not been using 1Password for my SSH keys before today ?
I've got a little further, with various API keys now stored in my 1Password vault
This is far simpler, in that the vault entry, of type API Credential, only needs to have a name/title e.g. IBM Cloud API Key and a credential, the actual API key itself.
With that in place, I've then setup an alias to retrieve/display the API key: -
apikey='export APIKEY=$(op item get "IBM Cloud" --field credential) && echo $APIKEY'
in ~/.zprofile, meaning that I just need to run the "command" apikey to ... see my API key.
I will, of course, be leveraging the same API keys in various other scripts/aliases, including things that login to IBM Cloud etc.
Visual Studio Code - Wow 🙀
Why did I not know that I can merely hit [cmd] [p] to bring up a search box allowing me to search my project e.g. a repo cloned from GitHub...

-
Whilst building a new "vanilla" Kubernetes 1.25.4 cluster, I'd started the kubelet service via: - systemctl start kubelet.se...
-
Why oh why do I forget this ? Running this command : - ldapsearch -h ad2012.uk.ibm.com -p 389 -D CN=bpmbind,CN=Users,DC=uk,DC=ibm,DC=com -w...
-
Error "ldap_sasl_interactive_bind_s: Unknown authentication method (-6)" on a LDAPSearch command ...Whilst building my mega Connections / Domino / Portal / Quickr / Sametime / WCM environment recently, I was using the LDAPSearch command tha...